Overview
The Digital Operational Resilience Act, or DORA, is a European Union (EU) regulation that creates a binding, comprehensive Information and Communication Technology (ICT) risk management framework for the EU financial sector. The act seeks to bolster digital resilience across financial institutions and their third-party technology service providers against ICT-related incidents and disruptions.
As of January 2025, DORA is fully enforceable and require strict compliance from financial institutions and ICT providers.

How Fortanix Helps
Fortanix delivers essential data security capabilities through a unified platform, enabling financial organizations and their ICT providers to identify at-risk services, prioritize remediation efforts, and safeguard sensitive data across all layers and systems—both on-premises and in the cloud.

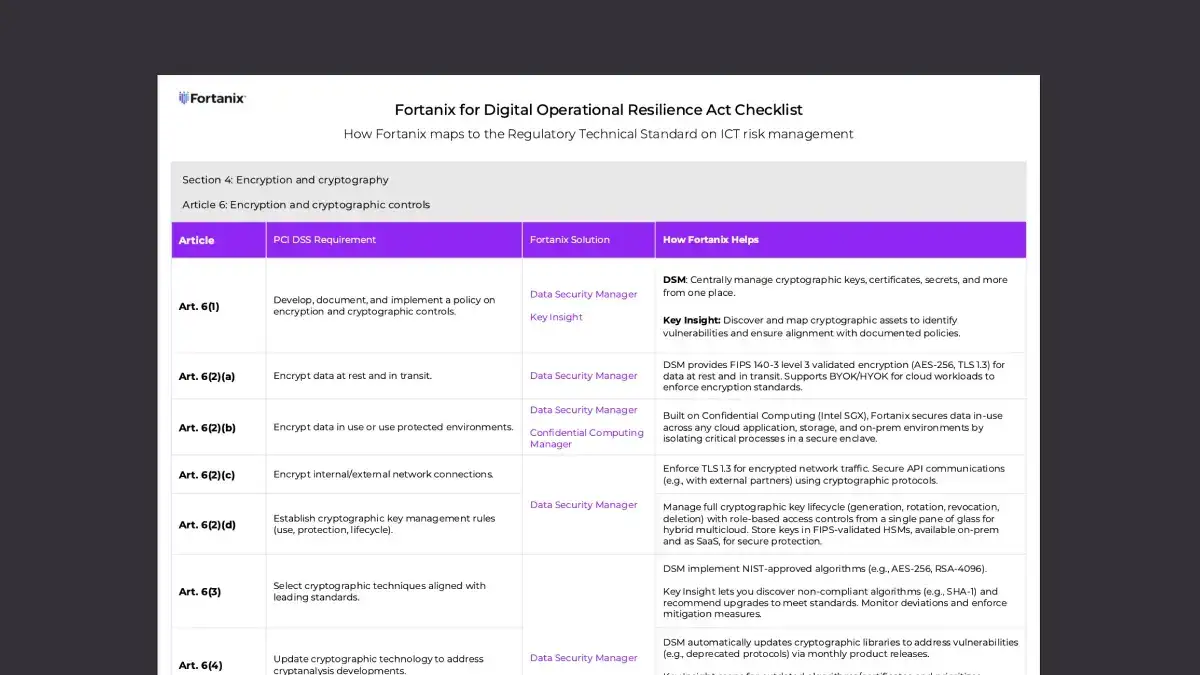
Cryptographic Posture Management
Manage assets and vulnerabilities by discovering, assessing, and remediating your encryption key security gaps. Get powerful insights into your cryptographic security posture across multi-cloud and on-prem environments for a complete inventory and visibility.

Data Encryption and Tokenization
Build resilient ICT risk management foundation. Encrypt data across databases, virtual machines, filesystems, and multi-cloud for complete security and compliance without performance loss and at scale. With data tokenization in place, replace sensitive data to prevent data exposure while putting it work.

Encryption Key Management
Meet cybersecurity requirements for cryptography with centralized and simplified key lifecycle management for the hybrid multicloud, through a single-pane-of-glass. Store keys in natively integrated FIPS 140-2 level 3 certified HSM, available on-premises or SaaS.

Zero Trust Architecture
Implement essential cybersecurity controls with granular Role-Based Access Controls and other advanced operational and security features. Ensure that only authorized users can access encryption keys or see decrypted data for a specified duration of the business case.
Resources


Blog
Achieving DORA Compliance: How Fortanix Strengthens Your Digital Operational Resilience

Blog
Public LLMs are The Hotel California for Data: Your Data Can Go in Anytime, but it Can Never Leave










