On November 20th, Fortanix announced integration between the Fortanix DSM with the Google Cloud External Key Manager (Cloud EKM) service in the session Bringing You More Control: New Services for Data Security and Transparency, featuring a demonstration by joint customer PayPal.
On the same day, I published Part 1 of the blog with an overview of the joint solution that enables enterprises using Google Cloud Platform (GCP) services including Big Query and Google Compute Engine (GCE) to maintain control of the master keys used to encrypt data.
In Part 2 of the blog, I’ll dive deeper into the technical details of how to set up and configure Cloud EKM with Fortanix, and how it supports Bring Your Own Key Management System (BYOKMS) for greater control.
Google Cloud Next UK Session with Google Cloud Product Manager Il-Sung Lee and PayPal Information Security Engineer, Greg King demonstrating the joint solution. Video starts at 19:13 for the PayPal demonstration.
Before we get into the technical details of the solution, the video below can provide you with a quick overview of the Cloud EKM service, the value to customers and how Fortanix integrates with GCP to manage master keys using BYOKMS.
Setting up Cloud EKM work with Fortanix DSM
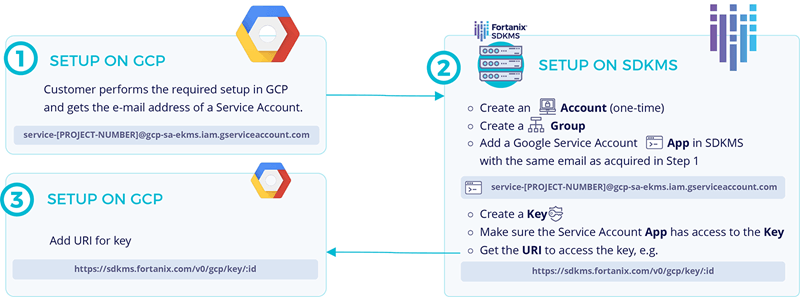
Cloud EKM has defined a set of REST APIs that an external key management system can implement. The APIs define the format for identifying the key held in the external KMS, and the operations that can be performed on the key. Fortanix DSM implements the Cloud EKM APIs, and supports the following configuration for BYOKMS deployments:
-
AES 256-bit keys stored in Fortanix DSM are identified by Cloud EKM using a URI, formatted as
https://DSM.fortanix.com/v0/gcp/key/<id>. The actual URI may depend on the domain specific to the Fortanix DSM deployment. -
Fortanix DSM supports performing encryption and decryption operations on these keys by making POST API calls on the following URIs -
https://DSM.fortanix.com/v0/gcp/key/<id>:wrapandhttps://DSM.fortanix.com/v0/gcp/key/<id>:unwrap. The request and response for these REST APIs are in JSON format. -
These API calls can only be made with the right authorization. This is obtained when authenticating to Fortanix DSM using a JSON Web Token (JWT) signed by the Google Cloud, which specifies the Google service account the request is originating from. The JWT can be verified by Fortanix DSM using Google Cloud’s public key.
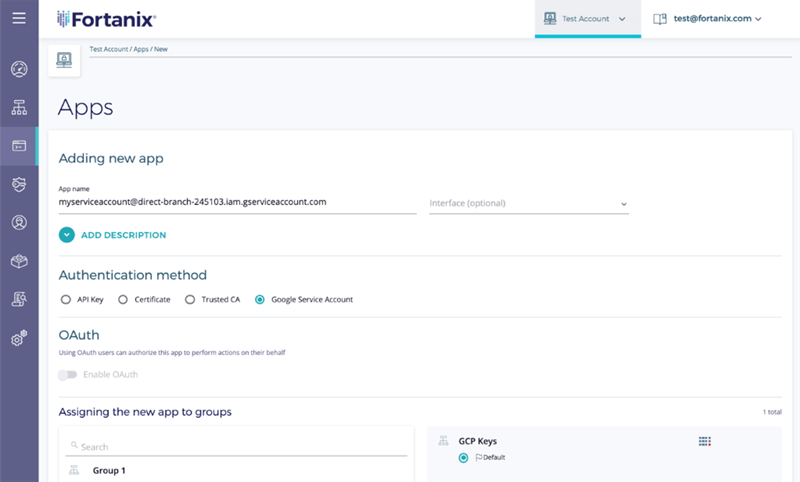
The service account name is used to determine which keys are accessible in a particular request. This access control requires an Fortanix DSM “application” to be created with the same name as the Google service account and added to an Fortanix DSM group containing the key which is being requested.
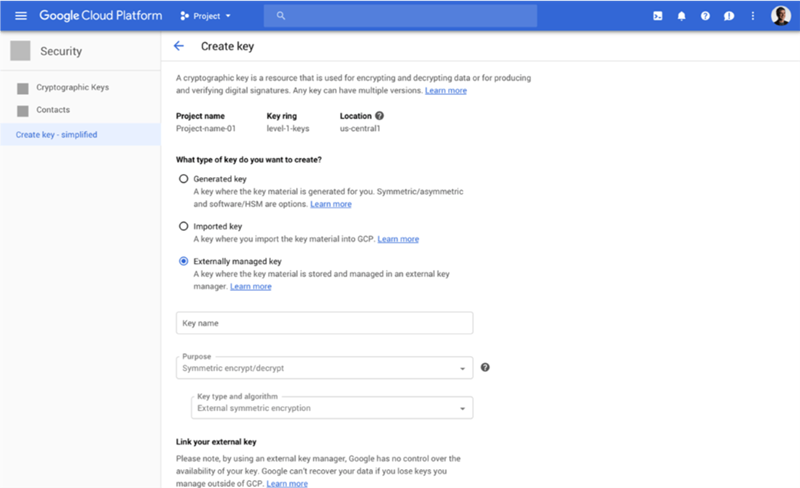
The corresponding configuration in Cloud KMS to access and externally managed key consists of the following:
-
A Google service account is created in GCP. The email address for this service account is used as an identifier of the request for Cloud EKM, and a corresponding application is created in Fortanix DSM with this email address as the name.
-
Once the application and key are created in Fortanix DSM, and the key URI is available, an externally managed key is created in Cloud KMS with the URI configured according to the above specification. This key gets a resource ID in GCP, which can be used by other GCP services as if it were any other key stored in Cloud KMS.
When a call is made to use an externally managed key in Google Cloud EKM makes a call to Fortanix DSM to authenticate itself and perform the requested operation. With BYOKMS, customers retain control of encryption keys.
Availability of Cloud EKM and Fortanix Integration
Cloud EKM is available today in beta on GCP. The Fortanix DSM integration is available immediately as an on-premises solution with a FIPS 140-2 Level 3 validated™ Fortanix Runtime Encryption Appliance, as software that can be deployed on-premises, and as SaaS offering through Equinix SmartKey, powered by Fortanix. TM: A Certification Mark of NIST, which does not imply product endorsement by NIST, the U.S. or Canadian Governments
Download this datasheet to learn how Fortanix External Key Manager generates and stores encryption keys outside of Google Cloud (GCP) and within customer datacenters.